Blog
Logging into OKX Spot Trading: Practical Truths, Common Myths, and What U.S. Traders Should Know
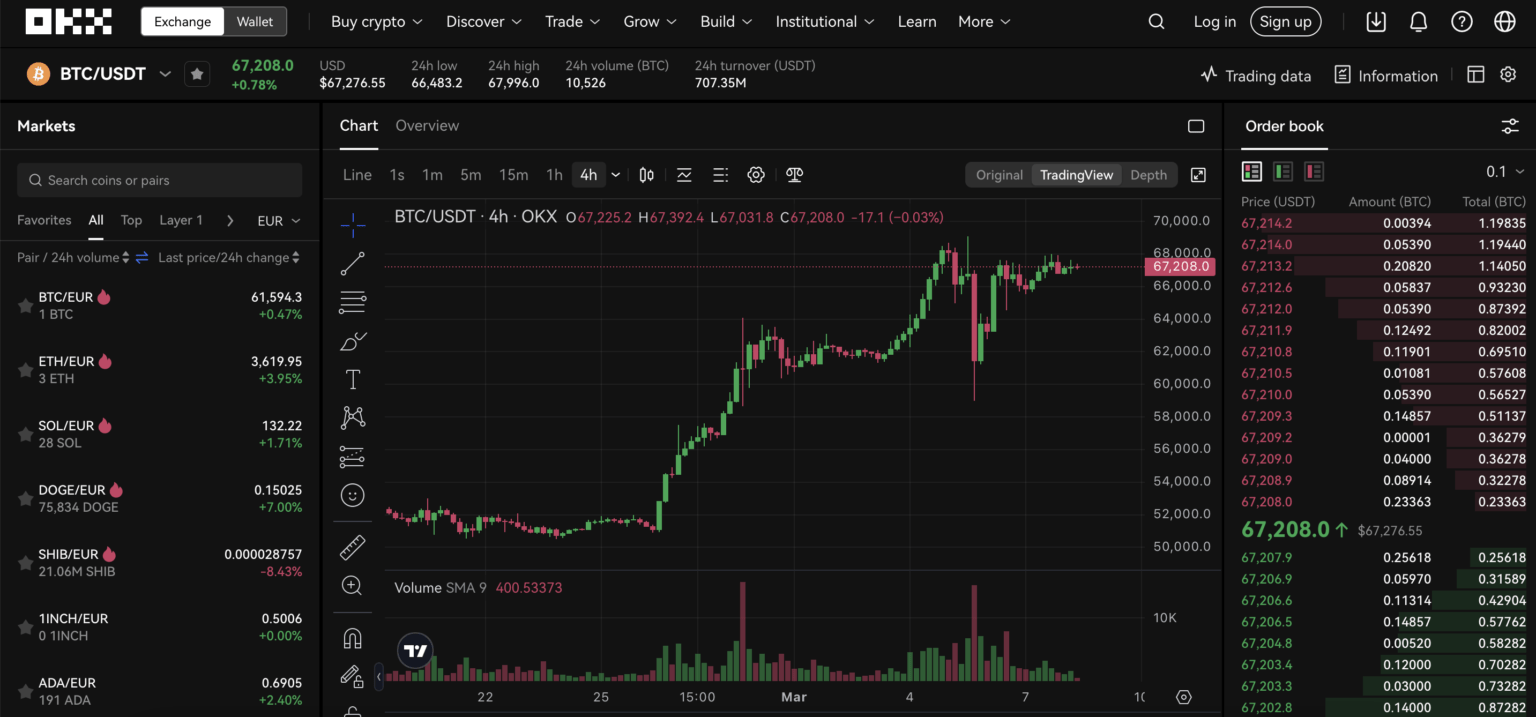
Imagine you wake before market open because a sudden USD-pegged stablecoin arbitrage has opened a narrow window. You have an OKX account, an order preset, and a mobile app—except you cannot log in. That concrete friction is the starting point for a deeper question: what does “logging in” to a modern crypto exchange like OKX actually involve, which assumptions traders get wrong, and how should that shape routine operational choices?
This article unpacks the mechanisms behind OKX account access (including KYC and two-factor protection), clarifies common misconceptions about custody and security, compares alternatives for where to keep trading capital, and ends with decision-useful heuristics and watch-points for U.S.-based traders. I’ll also point you to a practical login resource when appropriate.
How OKX login and account security actually work
At a mechanistic level, logging into OKX is not a single binary step but a sequence of layered checks that combine authentication, device/behavior detection, and regulatory identity verification. Step one is credential authentication (email/phone + password). Step two is mandatory Two-Factor Authentication (2FA) using SMS, an authenticator app, or biometrics on mobile. Step three is device and session risk scoring: OKX applies military-grade encryption plus AI-driven real-time threat detection to flag unusual login patterns. If you have not completed identity verification (KYC) you may still access limited features, but deposit, full spot, and margin capabilities are gated until KYC completes.
For U.S. users the practical consequences are immediate: anti-money-laundering (AML) rules require government ID and a liveness facial check to reach full functionality. That means if you plan to trade spot or margin, KYC timing matters. Adding funds the day you plan to execute a trade risks delay if the verification queue is backed up or if your selfie photo fails the automated checks. Consider KYC an operational dependency, not a formality.
Myths and corrections
Myth 1: “If I can log in, my funds are safe.” Partial truth. Login establishes control over the account UI and API access, but it is separate from where assets are stored. OKX stores over 95% of user assets in multi-signature, air-gapped cold storage. That reduces systemic hacking risk at the exchange level. However, account-level vulnerabilities—phishing, credential reuse, SIM swap attacks—still allow adversaries to move assets if they gain authenticated access and pass exchange withdrawal controls. So logging in is necessary but not sufficient for fund safety.
Myth 2: “Non-custodial wallet eliminates all risk.” False. OKX’s non-custodial Web3 wallet gives you full private key control, and hardware integrations (Ledger, Trezor) reduce custodial exposure. But self-custody shifts risks from the exchange (custodial hacks) to user error (lost seed phrases) and to smart-contract vulnerabilities when interacting with DeFi. The correct mental model: custody choice trades institutional security measures for personal responsibility and different attack surfaces.
Myth 3: “If a token is listed on OKX, it’s safe and liquid.” Not true. OKX supports 300+ assets and routinely adjusts listings; for example, in March 2026 it delisted several spot pairs as part of routine maintenance. Listing implies due diligence but not guaranteed liquidity or long-term support. Low-volume assets can still experience slippage and wide spreads even on a major exchange.
Where common login problems originate — and how to prevent them
Operationally, login failures come from five root causes: incorrect credentials, 2FA issues, device or IP risk flags, KYC holds, and account-level suspensions (e.g., security locks). The U.S. context introduces extra KYC friction because identity databases and government ID formats vary state-to-state, and automated liveness checks sometimes trip on lighting, camera quality, or facial accessories.
Practical mitigations: (1) complete KYC during quiet hours well before trading needs; (2) enable and separately secure an authenticator app rather than relying on SMS because SIM-swap is a real attack vector; (3) register and name devices you use frequently and keep a recovery plan for lost 2FA devices (print recovery codes and store securely offline); and (4) do a practice withdrawal when you first fund the account, using a small amount, so withdrawal whitelists and cold-wallet approvals do not surprise you mid-trade.
Trade-offs: custody, convenience, and access to advanced spot features
Traders choose between three practical custody states: fully custodial (hold funds on OKX), hybrid (use OKX non-custodial wallet/hardware), and full self-custody (external wallets/hardware). Each has trade-offs:
- Custodial (OKX): fastest market access, integrated staking/yield, and margin/derivatives. Drawback: you rely on exchange security practices and on-proof-of-reserves transparency rather than direct ownership.
- Hybrid: you retain control for some assets via the OKX Web3 wallet while keeping trading capital on-exchange. Good for separating long-term holdings from short-term trading capital. Drawback: more operational complexity.
- Full self-custody: maximum control and protection from exchange failures, but slower to deploy into spot trades and requires technical discipline to avoid seed loss.
For U.S. active spot traders who value immediate execution and access to staking or yield features (flexible staking, lock-up options, and auto-compounding), custody on OKX will often be the pragmatic choice. But remember: custody choice is a risk allocation decision, not a moral one—what you sacrifice in custody you gain in speed and product access.
Specifics for spot trading flows and login interactions
Spot trading on OKX is market execution at current prices; margin enlarges exposure with up to 10x leverage for certain trades. From an access perspective, spot trades require an active, KYC-verified account with available balance and a responsive session token. API traders should use API keys with limited scopes and IP-whitelisting; losing an API key is materially different from losing account credentials because keys can be scoped to trade-only (no withdrawals).
One operational nuance: during volatile moves, the exchange may enforce circuit breakers or temporary withdrawal cooldowns to protect users. Those mechanisms can appear suddenly after delistings, network congestion, or extreme price swings. If your strategy depends on rapid entry/exit, plan for these platform-level constraints and maintain a fallback (e.g., a second verified exchange or a small emergency self-custodied reserve).
Decision heuristics: when to log in, when to preposition funds, and when to split custody
Here are three heuristics you can reuse:
- If you need sub-second execution for spot arbitrage, keep minimal required capital custodial on-exchange with strict 2FA and withdrawal whitelists; rehearse login recovery processes.
- If your horizon is multi-week staking or yield farming, consider non-custodial flows or long-term holding on-chain with hardware backups; only move tradable slices to the exchange.
- Always separate “trading” wallet (funds sized to your worst-case intraday loss) from “reserve” wallet (cold or hardware), and document the recovery steps so you can act under time pressure.
If you want a practical walkthrough of the OKX web login flow and quick tips for avoiding common traps, use this resource for step-by-step guidance: okx login.
Limitations, unresolved questions, and what to watch next
Even with robust platform measures—cold storage for the majority of assets, Proof of Reserves transparency, and AI threat detection—there are open questions. Proof of Reserves demonstrates backing at a point in time but is not a continuous guarantee of liquidity under stress. AI threat detection reduces false negatives, but will always be reactive to novel phishing or social-engineering techniques. Delistings (like the recent removal of several spot pairs) remind traders that asset availability is a moving policy decision rather than a fixed property.
Signals to monitor: (1) regulatory changes in the U.S. around custody and stablecoin treatment; new rules could change KYC friction or product availability. (2) Changes to withdrawal approval workflows—shorter cold-wallet signing windows or different multi-sig policies materially affect execution risk. (3) Platform delisting notices and liquidity metrics for assets you trade; low liquidity often precedes delisting decisions.
FAQ
Q: Can I trade spot immediately after creating an OKX account?
A: Not necessarily. You can create an account quickly, but to use full spot and margin features or to make large deposits/withdrawals you must complete KYC. For U.S. users this includes submitting a government ID and a facial liveness check. Start and finish KYC before you need to execute time-sensitive trades.
Q: What should I do if I lose access to my 2FA device?
A: Use your printed/stored recovery codes to regain access, or follow OKX’s account recovery process which may require additional identity verification. To avoid this scenario, register multiple 2FA methods and keep one recovery copy in an offline, secure location.
Q: Is logging into the OKX mobile app safer than the web interface?
A: Both interfaces implement similar security controls, including biometrics on mobile. Mobile biometric login reduces password exposure, but phones are also targets for SIM-swap and malware. Practice device hygiene: update OS, avoid installing untrusted apps, and enable biometric + authenticator 2FA for layered protection.
Q: How do delistings affect my logged-in trading session?
A: Delistings can close new order entry for specific pairs and may place withdrawal or conversion windows around affected assets. If you hold a delisted asset, check exchange communications; you may need to convert or withdraw before final removal. Delistings are an example of exchange-level policy risk that affects trading ability irrespective of login status.
Bottom line: logging into OKX is both a technical sequence and an operational practice. Treat access control, KYC, and custody as three linked systems rather than discrete chores. That framing helps you design resilient routines: pre-verify identity, split custody by function, automate safer 2FA, and keep a minimal operational reserve on-exchange for time-sensitive trades. Those steps won’t eliminate market risk—but they reduce the friction and human error that so often turns a small opportunity into a missed one.
